Brace yourselves, Grandfather of Stuxnet media news are coming!
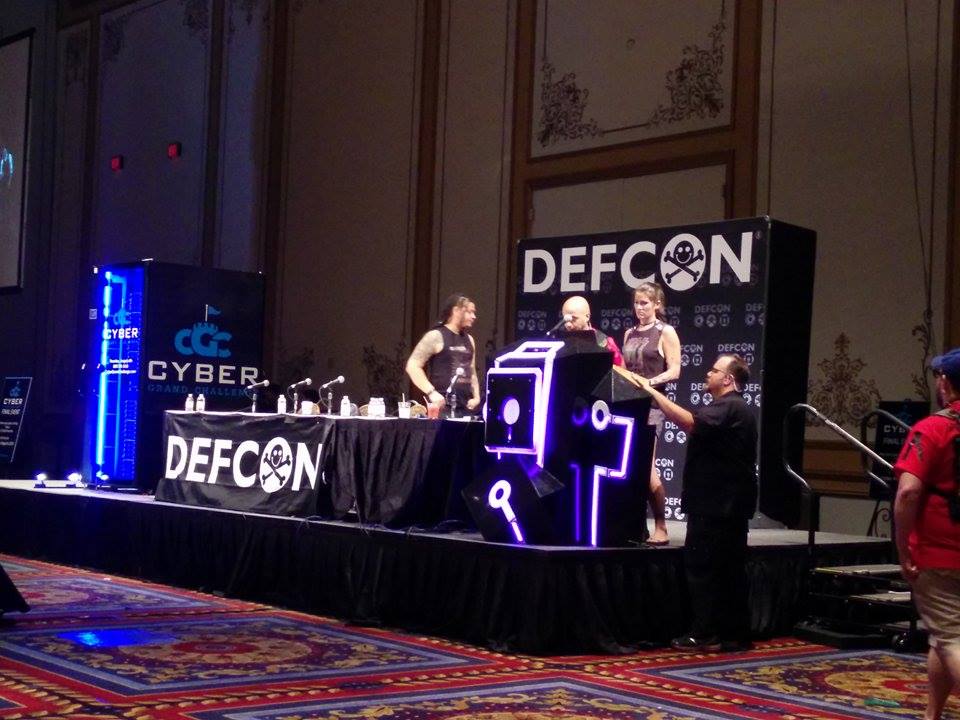
Today @pinkflawd and @headhntr gave a wonderful talk at Defcon about state sponsored attack and the (bad)state of attribution.
Saturday noon @headhntr & me be snarling again about the nefarious nation state malware biz at #DEFCON LV https://t.co/pXg6tZLyFf
— Mari0n (@pinkflawd) August 7, 2015https://www.defcon.org/html/defcon-23/dc-23-speakers.html#Marquis-Boire
Amongst the many great things they talked about, for me the “tipping point” was the revelation of rusty and hidden campaign dubbed Cheshire Cat targeting Windows NT systems using the notorious ~D prefix which tries to avoid only kaspersky AV.
Quick look at the samples provided in their keynote showing that (as usual) none of the AV vendors detected the malwares during that time.
https://www.virustotal.com/en/file/dc18850d065ff6a8364421a9c8f9dd5fcce6c7567f4881466cee00e5cd0c7aa8/analysis/
ec41b029c3ff4147b6a5252cb8b659f851f4538d4af0a574f7e16bc1cd14a300
https://www.virustotal.com/en/file/32159d2a16397823bc882ddd3cd77ecdbabe0fde934e62f297b8ff4d7b89832a/analysis/
https://www.virustotal.com/en/file/63735d555f219765d486b3d253e39bd316bbcb1c0ec595ea45ddf6e419bef3cb/analysis/
https://www.virustotal.com/en/file/c074aeef97ce81e8c68b7376b124546cabf40e2cd3aff1719d9daa6c3f780532/analysis/
If (like me) you wanna find out what its all about feel free to download them from here: https://s3-us-west-2.amazonaws.com/grandfatherstuxnet/CheshireCat.7z password: standard industry one.
Let me know what you find out (:
Update : Part of the research and key note is now on blackhat website - https://www.blackhat.com/docs/us-15/materials/us-15-MarquisBoire-Big-Game-Hunting-The-Peculiarities-Of-Nation-State-Malware-Research.pdf
Full keynote is now (26/08/2015) live on youtube: